| 일 | 월 | 화 | 수 | 목 | 금 | 토 |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | 4 | 5 | 6 | |
| 7 | 8 | 9 | 10 | 11 | 12 | 13 |
| 14 | 15 | 16 | 17 | 18 | 19 | 20 |
| 21 | 22 | 23 | 24 | 25 | 26 | 27 |
| 28 | 29 | 30 |
- Linux
- port
- VMware
- docker registry
- ssh
- 우분투
- RUBY
- opsworks
- 루비
- sudo
- AWS
- driver
- 리눅스
- golang
- Chef
- 드라이버
- VPN
- ssh command
- 방화벽체크
- window size
- ubuntu
- docker-compose
- 패키지
- DevOps
- docker container
- docker
- VIM
- QT
- Openswan
- 도커
- Today
- Total
구리의 창고
AWS Site-To-Site VPN <> Openswan 연결 본문
개요
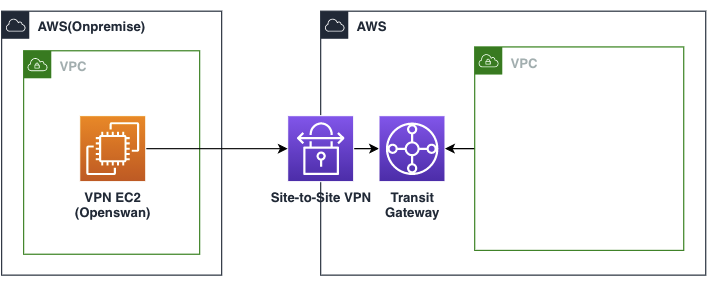
AWS Site-To-Site VPN은 IPsec VPN 서비스이다. 운영환경에 이용하기 적합하지는 않지만, 이를 이용하면 온프렘과 네트워크를 연결하고 테스트 환경을 쉽게 구축 할 수 있다. 아래와 같이 가상의 온프렘을 AWS VPC와 EC2를 이용해 구축하고, TransitGateway를 통해 VPN과 연결한다.
Openswan
오픈소스 기반의 IPsec VPN인 Openswan을 이용해 환경을 구축해보려고한다. BGP 설정을 위해서는 더 많은 작업들이 필요하지만, 이 글에서는 Static route 기반으로 구축하도록한다.
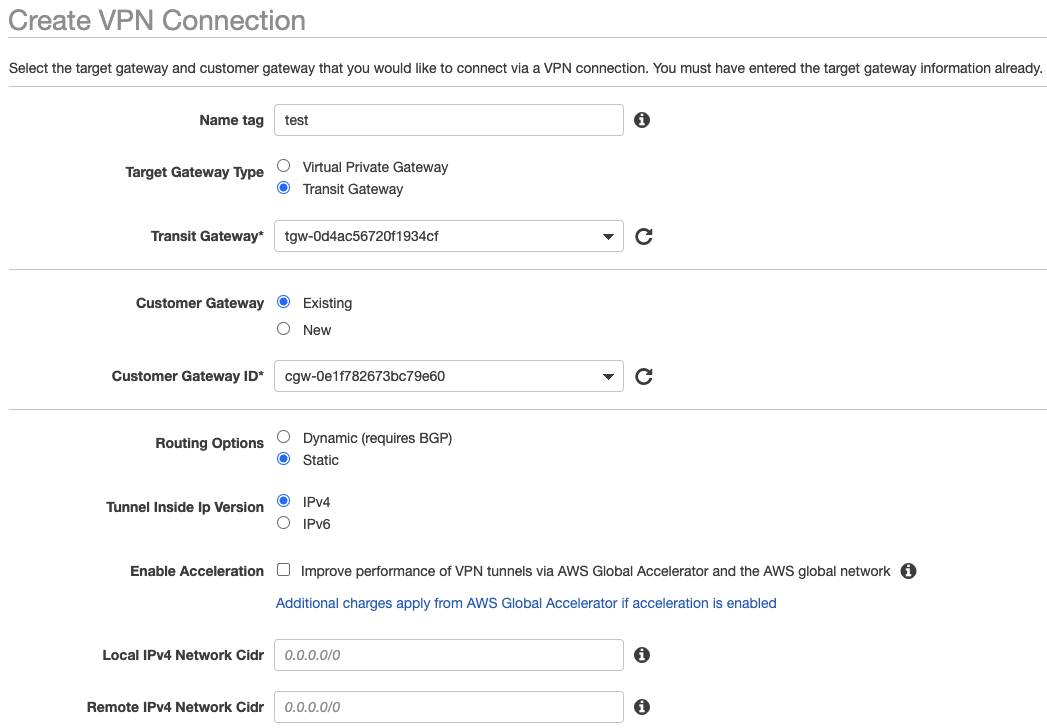
단계1: AWS Site-To-Site VPN 생성
Site-To-Site VPN과 TransitGateway를 아래와같이 terraform을 이용해 만들어준다. Openswan은 BGP를 지원하지 않으므로 static_routes_only 옵션을 반드시 활성화 하도록 한다.
resource "aws_ec2_transit_gateway" "this" {
auto_accept_shared_attachments = "enable"
default_route_table_association = "disable"
default_route_table_propagation = "disable"
}
resource "aws_ec2_transit_gateway_route_table" "this" {
transit_gateway_id = aws_ec2_transit_gateway.this.id
}
resource "aws_customer_gateway" "this" {
bgp_asn = 65000
ip_address = aws_eip.onprem.public_ip
type = "ipsec.1"
}
resource "aws_vpn_connection" "this" {
customer_gateway_id = aws_customer_gateway.this.id
transit_gateway_id = aws_ec2_transit_gateway.this.id
type = "ipsec.1"
static_routes_only = true
}AWS Console에서 생성하는 옵션을 살펴보면 아래와같다.
단계2: AWS Site-To-Site VPN 설정 확인
AWS Console > Site-To-Site VPN Connections 화면을 살펴보면 새로운 VPN이 생성된 것을 확인 할 수 있다. 방금 생성한 VPN을 선택하고 Download Configuration을 눌러서 설정을 내려받도록한다.

vpn-xxxxxxxxxxxx.txt 파일을 확인 할 수 있는데, 이 파일에는 2개의 터널 설정 정보가 담겨있다. 여기서는 터널 1개만 올릴 예정이므로 IPSec Tunnel #1를 사용하도록 한다. 다음 항목들을 메모하도록하자.
- Pre-Shared Key (AWS에서 생성된 값)
- Customer Gateway (온프렘 VPC Openswan의 Public IP, 여기서는 EIP)
- Virtual Private Gateway (AWS에서 생성된 VPN 터널의 Public IP)
IPSec Tunnel #1
================================================================================
#1: Internet Key Exchange Configuration
Configure the IKE SA as follows:
Please note, these sample configurations are for the minimum requirement of AES128, SHA1, and DH Group 2.
Category "VPN" connections in the GovCloud region have a minimum requirement of AES128, SHA2, and DH Group 14.
You will need to modify these sample configuration files to take advantage of AES256, SHA256, or other DH groups like 2, 14-18, 22, 23, and 24.
NOTE: If you customized tunnel options when creating or modifying your VPN connection, you may need to modify these sample configurations to match the custom settings for your tunnels.
Higher parameters are only available for VPNs of category "VPN," and not for "VPN-Classic".
The address of the external interface for your customer gateway must be a static address.
Your customer gateway may reside behind a device performing network address translation (NAT).
To ensure that NAT traversal (NAT-T) can function, you must adjust your firewall !rules to unblock UDP port 4500.
| If not behind NAT, and you are not using an Accelerated VPN, we recommend disabling NAT-T. If you are using an Accelerated VPN, make sure that NAT-T is enabled.
- IKE version : IKEv1
- Authentication Method : Pre-Shared Key
- Pre-Shared Key : UdRFA9AbvcSXfcjIuWiIggrSQfhvJ9oJ
- Authentication Algorithm : sha1
- Encryption Algorithm : aes-128-cbc
- Lifetime : 28800 seconds
- Phase 1 Negotiation Mode : main
- Diffie-Hellman : Group 2
#2: IPSec Configuration
Configure the IPSec SA as follows:
Category "VPN" connections in the GovCloud region have a minimum requirement of AES128, SHA2, and DH Group 14.
Please note, you may use these additionally supported IPSec parameters for encryption like AES256 and other DH groups like 2, 5, 14-18, 22, 23, and 24.
NOTE: If you customized tunnel options when creating or modifying your VPN connection, you may need to modify these sample configurations to match the custom settings for your tunnels.
Higher parameters are only available for VPNs of category "VPN," and not for "VPN-Classic".
- Protocol : esp
- Authentication Algorithm : hmac-sha1-96
- Encryption Algorithm : aes-128-cbc
- Lifetime : 3600 seconds
- Mode : tunnel
- Perfect Forward Secrecy : Diffie-Hellman Group 2
IPSec Dead Peer Detection (DPD) will be enabled on the AWS Endpoint. We
recommend configuring DPD on your endpoint as follows:
- DPD Interval : 10
- DPD Retries : 3
IPSec ESP (Encapsulating Security Payload) inserts additional
headers to transmit packets. These headers require additional space,
which reduces the amount of space available to transmit application data.
To limit the impact of this behavior, we recommend the following
configuration on your Customer Gateway:
- TCP MSS Adjustment : 1379 bytes
- Clear Don't Fragment Bit : enabled
- Fragmentation : Before encryption
#3: Tunnel Interface Configuration
Your Customer Gateway must be configured with a tunnel interface that is
associated with the IPSec tunnel. All traffic transmitted to the tunnel
interface is encrypted and transmitted to the Virtual Private Gateway.
The Customer Gateway and Virtual Private Gateway each have two addresses that relate
to this IPSec tunnel. Each contains an outside address, upon which encrypted
traffic is exchanged. Each also contain an inside address associated with
the tunnel interface.
The Customer Gateway outside IP address was provided when the Customer Gateway
was created. Changing the IP address requires the creation of a new
Customer Gateway.
The Customer Gateway inside IP address should be configured on your tunnel
interface.
Outside IP Addresses:
- Customer Gateway : 13.125.83.100
- Virtual Private Gateway : 3.34.244.100
Inside IP Addresses
- Customer Gateway : 169.254.227.170/30
- Virtual Private Gateway : 169.254.227.169/30
Configure your tunnel to fragment at the optimal size:
- Tunnel interface MTU : 1436 bytes
#4: Static Routing Configuration:
To route traffic between your internal network and your VPC,
you will need a static route added to your router.
Static Route Configuration Options:
- Next hop : 169.254.227.169
You should add static routes towards your internal network on the VGW.
The VGW will then send traffic towards your internal network over
the tunnels.단계3: Openswan 설치
설치 스크립트는 다음과 같다. 스크립트를 실행하면 /etc/ipsec.d/tunnel.conf, /etc/ipsec.d/tunnel.secrets 에 설정이 만들어진다.
#!/bin/bash
read -p "Left IP(VPN IP): " LEFT_IP
read -p "Left CIDR(VPN CIDR): " LEFT_CIDR
read -p "Right IP(AWS IP): " RIGHT_IP
read -p "Right CIDR(AWS CIDR): " RIGHT_CIDR
read -p "VPN Secrets: " SECRETS
echo
yum install -y openswan
cat <<EOF > /etc/ipsec.d/tunnel.conf
conn tunnel1
authby = secret
auto = start
left = %defaultroute
leftid = $LEFT_IP
right = $RIGHT_IP
type = tunnel
ikelifetime = 8h
keylife = 1h
phase2alg = aes128-sha1;modp1024
ike = aes128-sha1;modp1024
keyingtries = %forever
keyexchange = ike
leftsubnet = $LEFT_CIDR
rightsubnet = $RIGHT_CIDR
dpddelay = 10
dpdtimeout = 30
dpdaction = restart_by_peer
EOF
cat <<EOF > /etc/ipsec.d/tunnel.secrets
$LEFT_IP $RIGHT_IP: PSK "$SECRETS"
EOF
cat <<EOF > /etc/sysctl.d/99-vpn.conf
net.ipv4.ip_forward = 1
net.ipv4.conf.default.rp_filter = 0
net.ipv4.conf.default.accept_source_route = 0
EOF
sysctl --system
service ipsec restart
sleep 5
ipsec status단계4: Openswan 연결 확인
아래와 같이 나온다면, VPN이 정상적으로 연결된 것이다.
$ ipsec status
000 Connection list:
000
000 "tunnel1": 10.100.0.0/16===10.100.0.238[13.125.83.100]---10.100.0.1...3.34.244.105<3.34.244.100>===10.0.0.0/16; erouted; eroute owner: #2
000 "tunnel1": oriented; my_ip=unset; their_ip=unset; my_updown=ipsec _updown;
000 "tunnel1": xauth us:none, xauth them:none, my_username=[any]; their_username=[any]
000 "tunnel1": our auth:secret, their auth:secret
000 "tunnel1": modecfg info: us:none, them:none, modecfg policy:push, dns:unset, domains:unset, banner:unset, cat:unset;
000 "tunnel1": labeled_ipsec:no;
000 "tunnel1": policy_label:unset;
000 "tunnel1": ike_life: 28800s; ipsec_life: 3600s; replay_window: 32; rekey_margin: 540s; rekey_fuzz: 100%; keyingtries: 0;
000 "tunnel1": retransmit-interval: 500ms; retransmit-timeout: 60s;
000 "tunnel1": initial-contact:no; cisco-unity:no; fake-strongswan:no; send-vendorid:no; send-no-esp-tfc:no;
000 "tunnel1": policy: PSK+ENCRYPT+TUNNEL+PFS+UP+IKEV1_ALLOW+IKEV2_ALLOW+SAREF_TRACK+IKE_FRAG_ALLOW+ESN_NO;
000 "tunnel1": conn_prio: 16,16; interface: eth0; metric: 0; mtu: unset; sa_prio:auto; sa_tfc:none;
000 "tunnel1": nflog-group: unset; mark: unset; vti-iface:unset; vti-routing:no; vti-shared:no; nic-offload:auto;
000 "tunnel1": our idtype: ID_IPV4_ADDR; our id=13.125.83.131; their idtype: ID_IPV4_ADDR; their id=3.34.244.105
000 "tunnel1": dpd: action:restart; delay:10; timeout:30; nat-t: encaps:auto; nat_keepalive:yes; ikev1_natt:both
000 "tunnel1": newest ISAKMP SA: #1; newest IPsec SA: #2;
000 "tunnel1": IKE algorithms: AES_CBC_128-HMAC_SHA1-MODP1024
000 "tunnel1": IKE algorithm newest: AES_CBC_128-HMAC_SHA1-MODP1024
000 "tunnel1": ESP algorithms: AES_CBC_128-HMAC_SHA1_96-MODP1024
000 "tunnel1": ESP algorithm newest: AES_CBC_128-HMAC_SHA1_96; pfsgroup=MODP1024
000
000 Total IPsec connections: loaded 1, active 1
000
000 State Information: DDoS cookies not required, Accepting new IKE connections
000 IKE SAs: total(1), half-open(0), open(0), authenticated(1), anonymous(0)
000 IPsec SAs: total(1), authenticated(1), anonymous(0)
000
000 #1: "tunnel1":4500 STATE_MAIN_I4 (ISAKMP SA established); EVENT_SA_REPLACE in 26379s; newest ISAKMP; lastdpd=7s(seq in:15226 out:0); idle; import:admin initiate
000 #2: "tunnel1":4500 STATE_QUICK_I2 (sent QI2, IPsec SA established); EVENT_SA_REPLACE in 1420s; newest IPSEC; eroute owner; isakmp#1; idle; import:admin initiate
000 #2: "tunnel1" esp.c62044bb@3.34.244.100 esp.bede1846@10.100.0.238 tun.0@3.34.244.100 tun.0@10.100.0.238 ref=0 refhim=0 Traffic: ESPin=0B ESPout=0B! ESPmax=4194303B
000
000 Bare Shunt list:
000
'AWS' 카테고리의 다른 글
| APEX - NoCredentialProviders: no valid providers in chain. Deprecated. (0) | 2017.09.13 |
|---|---|
| AWS Opsworks - Chef11 vs Chef12 차이점 (0) | 2017.09.05 |
| AWS Opsworks Chef11 - Custom Cookbook Debugging (0) | 2017.09.02 |

